Home Lab Environment for Security Testing

Why Build a Home Lab for Security Testing? In the Cyber Security field, theoretical and book knowledge pales in comparison to the insight gained from hands-on experience and doing the thing. This article kicks off a series dedicated to those wanting to get started in this field, or those who are already working in the field […]
Mobile Device Security – Tips and Tricks for General Users

Mobile Device Security – Tips and Tricks for General Users: a post in a series of articles for general endusers to better protect themselves online. In today’s world, our mobile devices have become an integral part of our daily lives. They store our personal information, allow us access to our finances and healthcare information, help […]
Backup & Encrypt: Secure your Digital Life

In today’s world, safeguarding your personal data is more important than ever. Cyber threats and data loss are a growing concern, and taking the necessary steps to protect your valuable information is crucial. In this post, I will guide you through the process of encrypting your data using BitLocker for Windows devices and FileVault for […]
Online Identity – Protecting yourself from Theft

In this digital age, protecting your online identity is essential. Cyber criminals are constantly on the lookout for ways to hack into your accounts and steal your sensitive information. One of the best ways to enhance your cybersecurity is to use strong, unique passwords for each of your online accounts and enable two-factor authentication (2FA) […]
Protecting yourself Online: A Beginner’s Guide for Information Security
In today’s digital age, information security is more important than ever. With cyber threats on the rise, it is crucial for everyday users to understand the basics of protecting their personal data. In this article, we will discuss key principles, strategies, and best practices to help you strengthen your online security. By the end of […]
Ransomware Detection & Response
Ransomware attacks have been on the rise in recent years, causing significant financial and operational disruptions for organizations across various sectors. This brief guide covers essential ransomware defense strategies, including understanding what ransomware is, implementing technology solutions and process controls, and preparing your organization to respond effectively to a ransomware attack. Ultimately, some of these […]
Risk Management or how high is that cliff?

Risk management is an indispensable element of cybersecurity for any organization. As the complexity and frequency of cyber threats continue to rise, implementing effective risk management practices becomes vital in protecting sensitive information, ensuring business continuity, and preserving an organization’s reputation. In this post, we will delve into the roles and responsibilities of various stakeholders […]
More OWASP fun with ChatGPT

Continuing to mess around with my research into things I can do with the ChatGPT-4 Large Language Model and training developers on some basics of the OWASP Top 10 secure coding vulnerabilities. In this week’s episode, I have expanded on the prompts I used in prior articles, and have gotten the AI to go deeper […]
Information Security Training: Why & How

Empowering Your Workforce to Safeguard Your Organization’s Digital Assets Introduction In today’s regulatory, litigious and online world, information security is a top priority for businesses of all sizes. With the increased reliance on technology and remote work, the potential for cyber threats is higher than ever. It is critical for organizations to invest in information […]
ChatGPT 4.0 – more blogging via Artificial Intelligence
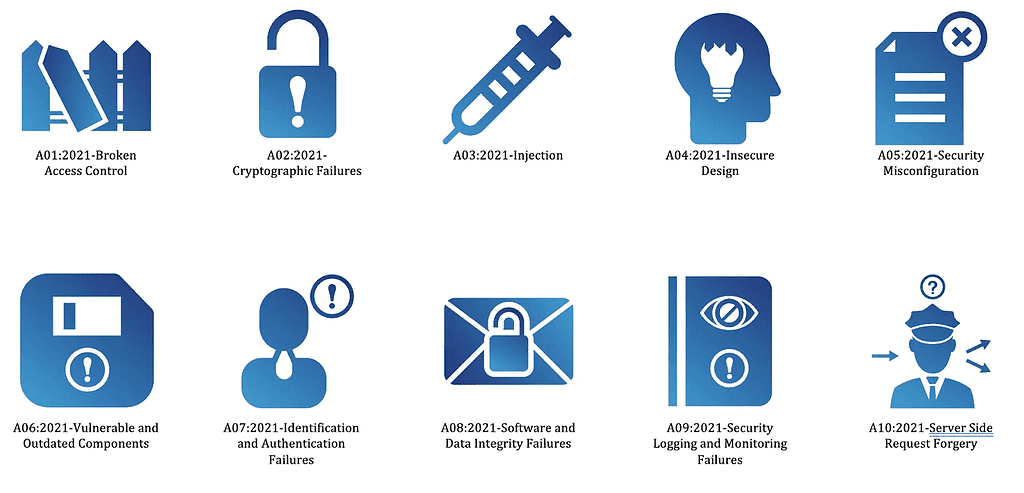
[Author’s Note] The following was part of my testing of artificial intelligence (specifically ChatGPT’s) ability to write technical blog posts and also create training materials for developers to better understand secure coding practices. I used ChatGPT 4.0 for this and may go back and refine the prompts I used to get more complex examples, but […]

